Mac OS FAQ |
Updated: 1 January 2024
If you have recently bought or set up a Mac then I suggest you take the following steps to secure your Mac:
1. Configure the Firewall
A firewall will block unwanted incoming and outgoing attacks to or from your computers. It will prevent trojans and worms attacking your Mac. Mac OS X has the Firewall installed, which blocks incoming and some outgoing connections , use that wherever possible if you don`t have a third party firewall.
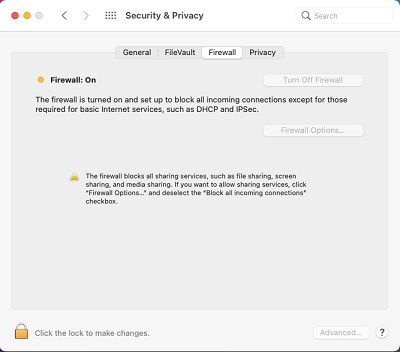
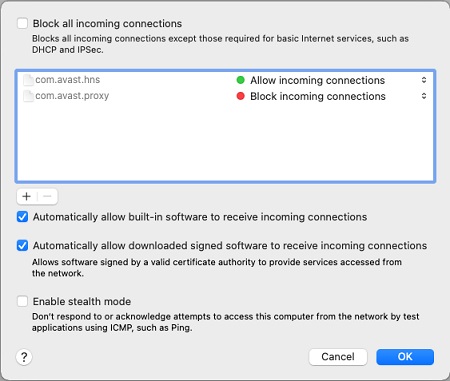
a) How to I allow other applications through the firewall?
Click the Firewall Options button, turn off Block all incoming connections, click the plus (+) sign to add further applications through.
2. Install an Anti-Virus Product.
Firewalls will protect against some forms of attack but not all. Viruses come
in all sorts of forms such as Macros, Programs, scripts and so on.
Only an antivirus
program will block and delete such threats. , there are many other anti-virus products
to list see, Product List.
For more information on viruses, see the Virus
Library on symptoms and removal instructions.
4. Configuring Security and Privacy in Safari
A lot of websites use suitable tricks to track and download private information
about your self and your web browsing habits and tend to install plugins and
programs that sometime hijack your browser to set your home page or display
pop ups. Also, in Safari in Secury and Privacy, turn on the Fraudulent Website Warning on.
You can also restrict the types of cookies saved to your PC via the options
in your Web Browser. For example, in Safari, use Settings, Privacy and set a block cookies level to suit your web sites ('Allow from website I visit'
is suitable in most cases). For lists of spyware or adware programs visit Removing SpyWare.
5. Clear out your History and Web site data and Cookies cache
Copies of web pages and pictures are saved in a cache on your PC, clearing this cache out on a regular basis (no more than once a week) will remove any unwanted files. In Safari goto Settings, Privacy and Security and click on Clear History and Website Data.
6. Use more secure file systems
Where possible use more secure file systems to encrypt data. You can do this on Mac OS by enabling the FileVault feature.
To turn it on go to System Preferences, Security and Privacy and select the FileVault tab, click on Turn on FileVault. If you loose your recovery key or account password then
it will be impossible to recover the data.
Make sure you backup your personal recovery key to a USB stick, because if you loose that and need to recover data, it will be impossible to read the data again.
If you just want to encrypt specific files or folders, then you can use the Disk Image from Folder feature in the Disk Utility to create a encrypted DMG image file from containing the files you want secure. See this article for more details on how to do this.
7. Keep your Mac up to date with latest security patches
Wherever possible keep your Mac updated with latest security updates from Settings, Software Update app, or visit the Apple Support website to download updates.
8. Backup your data
Get a decent backup program in case your Mac is infected, attacked or otherwise made unusable and require a reinstall. Programs are easily to reinstall but data is very hard to get back if deleted, overwritten or lost. A free backup tool is provided called Time Machine.
9. Secure Mac with usernames and passwords or fingerprints
Use a standard user than an Administrator user when using your Mac. Also, make sure that you always set a password for accounts including the administrator account, which is blank by default on most Destkop systems. Never write passwords down where they can be easily found and use complex passwords, using combinations of letters and digits and do not use personal information for passwords e.g. names, date of births, pets etc. which can be easily broken.
Never give out personal information such as account details, pins numbers or passwords from Emails sent over the network. Legitimate companies and banks will never ask for such information even if threatened with Account closure or suspension and never click on links provided on such Emails as they will always be sent to fake web sites.
If you Mac is a MacBook, then you can secure it by using your fingerprint on the Touch ID button (usually at the top right).
10. Clear out your Contacts
A lot of viruses now uses your contacts to spread itself to other users. I suggest you delete any unwanted or old email contacts from your Address Book now and again.
11. Do not use Peer-to-Peer File Sharing Software.
File sharing software basically allows anyone to read files off your computer and bypasses your Firewall and all other security considerations. Consider this as a very risky. If so, do NOT login with an account which has administrator privileges, and apply strict permissions to the folder you use for file sharing and keep it well away from any personal data.
If using NAS drives make sure that they use the more secure AFP or SMB2 protocol. Also, do not have smb shares connected to Mac desktop for long periods. Malware such as encryption (aka Ransomware) are known to encrypt data on hard disks and any connected storage.
12. Do not advertise your email address.
Your email address can be searched for and use for spam very easily by programs that actively look for email addresses than can be used to spread spam. If you have your own web site DO NOT use the standard technique of using HREF and the MAILTO: method of displaying your email address, instead use Javascript to hide it from spammers and search programs (called webbots). If you visit a website and need to create a profile or login name, if it asks for an email address either enable the option to hide the address from public view or use another email address instead of your main email address.
13. Erase your hard disk before selling or recycling your old Mac.
Programs and data can be easily stolen from hard drives on old PCs.A format will not clear it, you need to overwrite the data several times with a good secure erasure program which will write loads of 00000s then 11111s and 1010101s. Use the Disk Utility and in the Erase tab enable some of the Security Options when erasing a disk. For more permanent destruction you could use a powerful magnet, a drill or a hammer to destroy the disk (only for the most paranoid users).
14. How can I secure my Wireless Network?
Wireless networks, if unsecured can be open for anyone to use and if you have an unsecure network, people can potentially view files on your shared folders.
To secure your wireless network, you should enable encryption of all network traffic using WPA2. You should also hide the name or SSID of your wireless network to prevent people trying to connect to it. Also, you can restrict the network to specific computers and mobile devices by putting them in a Wireless Station Access List so that unknown devices cannot connect. It is also a good idea to change the router's default admin password to prevent others from changing its settings and locking you out.
Go to Web Browsers